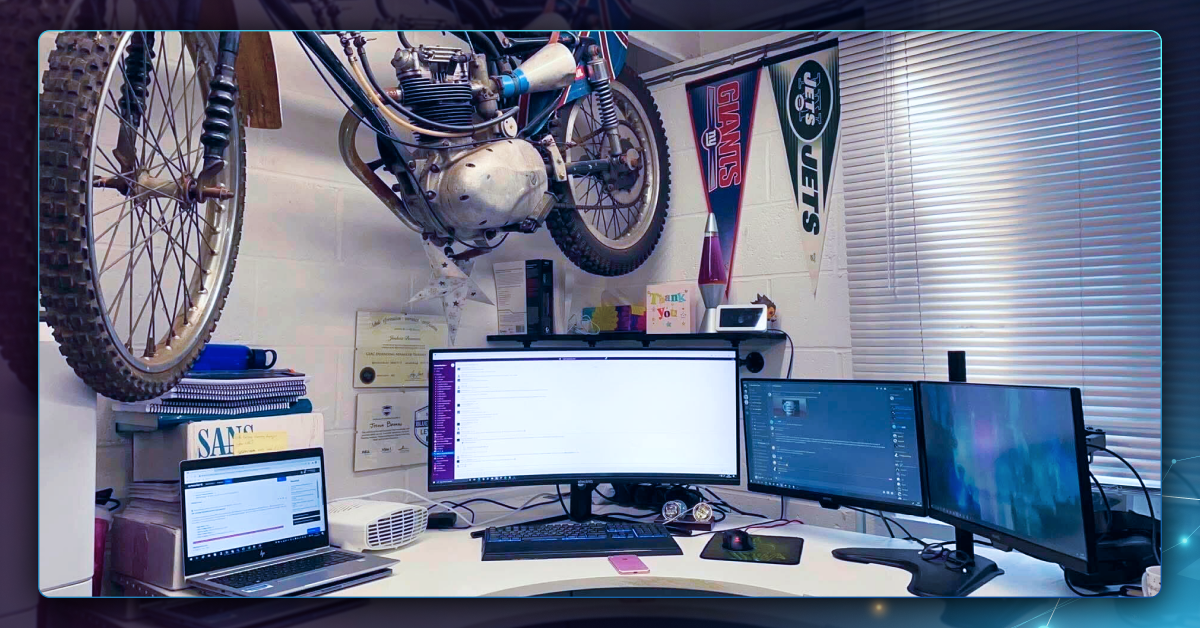
Meet Duncan: One of SBT’s Marketing Executives Bringing Stories to Life
Get to know Duncan Whitley, one of Security Blue Team’s Marketing Executives, who creates blog posts, newsletters, emails, and ads to deliver genuinely useful cybersecurity content. From a background shaped by gaming and technology to a career in marketing, Duncan shares why he values clear, helpful communication and enjoys seeing...